First published: 23 October 2014
Latest Revision: 3 January 2024
FUNCTIONAL REQUIREMENTS
The network architecture is designed to support all HIS applications discussed earlier and achieve the following objectives:
- Allow data communications between all applications and users of the entire system.
- Ensure quick response to requests (fast system performance) and ensure completion of transactions.
- Ensure business continuity (almost 100% up-time through sufficient redundancy and system back-up)
- Fully recovery from a disaster (system may be re-built from back-up of data, system configuration and restoration of applications)
- Storage capacity capable of holding current data and additional data for the next 5 years.
- Scalability of memory and server-storage hardware.
ARCHITECTURE DESIGN: LAYOUT AND COMPONENTS
Since the HIS consists of many sub-systems, has many components and used by many users, the most appropriate architecture is that of the client-server layout (configuration). Even a system for a general practice clinic would need a system that is used by at least three users (the doctor, nurse and receptionist). They may each have a computer that is linked to one another (peer-to-peer system) allowing them to access data on them. However, a client-server is better because the management of data is better served if data is stored in and accessed from a common database as in system.
Client-Server Configuration
The information system for a single clinic or hospital is best built around a Multi-tiered Client-Server on a Local Area Network (LAN) architecture. The tiers refer to:
- the front-end where the user uses a computer (e.g. personal computer, hand phone) to view and enter data
- the applications used to conduct the business of caring for the patient
- the mechanism of storing data and making it available
Clients
If the computer system is considered as a service provider, then the people that it serves will be its clients. However, the term user is used for the person using the computer. The term client refers to the front-end computer hardware and the software that it contains. The client software or an internet browser enables the user to access and use applications to perform their work.
Clients are computers usually a personal computer (PC) or hand-phone with display monitors and data input devices such as keyboard, scanners, readers and mouse, plus the operating system to run them.
Server
In common usage, a server is a person who attends to requests by customers (clients), forward it to responsible parties and later hand over what was requested when it is ready. Computers can also be designed to provide such a service. Users can request for applications or data from a computer acting as a server. Hence there two main types of servers:
- Applications server
- Data server
Because servers have to respond to many users, they are usually high end computers with adequate memory and storage space.
Data Server
The data server acts as an intermediary between the client, the Database Management System (DBMS) and the data storage devices (hard disks or tapes). All the tiers are linked through a network consisting of cables joined by switches and routers. Part of the network can also be wireless.
Applications Server
With regards to access to applications, the client-server network can be configured according to
- the thick-client configuration.
- thin client configuration.

Different Ways to Configure the Client-Server Architecture
Thin-Client Configuration
A thin client computer would provide only a small part of the applications used to perform work. As such it need not be a high-end computer but one that can work as a workstation will do. However, in a HIS it is preferable to use a PC even for this purpose because it would give better displays for graphics, something important in a hospital information system. The main part of the applications resides in the Applications server which have sufficient memory and storage capacity (disk-space) to accommodate various applications. Users request for part of or the entire application when they need it. They, then, can submit and retrieve data through the Application server which acts as an intermediary between them and the Data server.

Thick Client Configuration
In the thick-client configuration the client computer is a high-end PC that can accommodate all applications. The thick client interacts directly with the database (DBMS) to submit and retrieve data.

The Network
All the tiers are linked through a network consisting of cables joined by switches and routers. Part of the network can also be wireless.
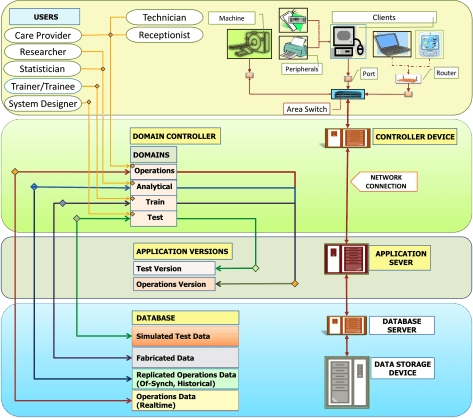
A typical thick-client network configuration of the HIS System Architecture implementation is shown below:
A typical thin client network configuration of the HIS System Architecture implementation is shown below:
Typical Thin-Client Client-Server HIS System Architecture
- A sufficiently fast processor
- Sufficient ready access memory (RAM) to retain data temporarily while being viewed or entered
- A display monitor for viewing both applications and data.
- Data input tools such keyboard, bar-code reader and image scanners and pointing devices e.g. mouse
- A front end Operating system (OS) that allow all the above hardware to function and to facilitate interaction with the server
- Video/graphic cards for locations where complex images are used
Hybrid Thin plus Thick Client Configuration
If a high end PC is used as the client, then both the thick and thin client configuration can be used. Some applications can be implemented in the thick client while others in the thin client configuration.
Client Computer Specifications
Generally, for clients, Desktop and Laptop/Tablet PCs with high end CPUs and sizeable memory are preferred. These can be used either as thick and thin clients or a hybrid. They are attached to the network through suitable cables and wireless connections.
For a thick client installation, client computers with fast CPUs and sizeable RAM memory is required. They are loaded fully or partially with Applications software.
In a thin client approach, the client is loaded only with a browser. The Applications are retrieved from the Applications server as and when they are needed. Lower end CPUs may be used and less RAM memory is required. However, in a HIS set-up, the hardware usually used as thin clients (low end computer with little processing power and memory) is not suitable because of the need to present images and graphs. Instead PCs are more appropriate. Each client can be used for a multitude of clinical and managerial (office automation, e-mail) applications and also as Image viewers. The operating system (OS) for the front end (presentation logic) must cater for all these applications. It should also support user interfaces (GUIs) that satisfies user needs.
Web-Based System
A web-based system is a variant of the thin-client configuration. The difference is that the Application and Database servers are located at a remote location (off-site). Data is transmitted via a wide area network (WAN) almost invariably the internet. It may be used for two reasons:
- a healthcare facility may locate applications and database servers in a data center outside of the hospital
- an enterprise with multiple facilities at different locations can make use of centralized applications and database servers housed in a single data center in one of its premises.
For both of the approaches the data center can be owned and managed by the facility or enterprise or by a third party vendor. A facility like a stand-alone hospital may prefer to use a data-center belonging to a third-party vendor because Web-based systems appeal to medical practices the hardware and data center need not be purchased but leased. Therefore the initial outlay for implementation is smaller and smaller payments need to be made on a staggered basis.
The vendor providing the services of hosting the servers and data storage devices may also provide the all the applications. The company is then referred to as ASP (application service provider) or SaaS (Software as a Service). the application belongs to the applications licensing company. The company will be responsible to procure, implement the software and maintain the licenses.
Because access to the servers is through the internet (usually a VPN), the company will also arrange for obtaining internet access service from one or more telecommunications company.
The Web service provider provides the data centre with hardware and system software including the web server and the reverse proxy server.
Using Web-Based System in a LAN
The system may adopt web technology within the local area network. A web client may be used to host the browser just like thin clients. If a care provider requires access to HIS via clients at locations outside of the hospital such as from home or another hospital / clinic, then it should be connected to the hospital’s LAN through a secure network such as Virtual Private Network (VPN).
System Functional Requirements
In a comprehensive integrated HIS, the server-storage system need to cater to both the managerial applications as well as the patient care applications. Because a hospital functions 24 hours a day, and everyday for 365 days a year, the system should not fail. Currently an uptime of 99.9% is the standard aimed for. To achieve this there should be duplication of the means to make applications available and to ensure that data can be saved and retrieved without interruption. This translates into the provision of more than one location where each application resides and where data is stored. The ability for the system to function if one part fails is termed as redundancy.In patient care, at any given time there are numerous users of the system causing heavy data traffic. Both the applications and database servers must have sufficient processing power and memory to deal with requests. The data required at anytime is usually great and a large amount of data accumulates over time. The storage device must have a large storage space and also able to accept and release data efficiently.Besides being used for day to day operations, a complete system need to cater for other functions. Therefore copies of applications and systems need to be provided for other important uses. The alternative versions of clinical applications and separate databases are often called ‘domains’. These usually include:
- Production or Operations Domain
- Analytical Domain
- Build or Test Domain
- Train Domain
The Operations Domain cater for day to day use where the data is actual and in real-time. The Analytical Domain allow actual but not necessarily real-time data to be analyzed to produce reports. The Build/test Domain contains a version of the applications often different from that of the operations environment. It may contain fabricated data. The Train Domain contains the same software version as the Operations Domain but only fictitious/fabricated data. Despite the many domains and versions, these do not necessarily mean that separate server-storage hardware are required.
APPLICATION SERVER
Servers cater for requests from users to:
- use an application or a part of it
- input or retrieve data
The Applications server(s) contains all Applications software and provides whatever applications the user wish to use. It integrates with the data storage function via the Storage (Database) server. Traditionally, the Managerial applications and the Clinical Applications use separate servers and storage systems. Together with the need for duplication, this may result in the provision of many physical servers and storage systems.The use of virtualization technology can reduce the number of physical servers. A cluster of physical servers (minimal two) may be used. Each physical server will house many virtual servers.
The Applications server hosts all the Applications software if the thin client approach is used. However, if PCs are used a portion may reside in the client computer.System Software / Operating System for the Server(yet to be written)
DATABASE AND DATA STORAGE HARDWARE
Database Server
Database/Storage servers control data input and output from storage devices such as Storage Area Network (SAN storage) or Network Area Storage (NAS). The software that defines the structure and content of the database is the Database Management System (DBMS). This can be of the relational, hierarchical or object-oriented types. The database server itself and the DBMS requires an appropriate system software (OS).Data Storage DeviceCurrently, the hardware that holds the data is a set of hard-disks (disk array). Magnetic tapes (tape library) are used mainly to archive data as back-up.NETWORK (Cables & Wireless)Hardware components of the various tiers of HIS are linked through a network (both cables and wireless). The network need to have the following features:
- Sufficient bandwidth corresponding to volume of data that will traverse through two points to be connected.
- Redundancy to ensure an alternative passage of data if one route is impassible
One way is to provide two single mode fibre optic cable as backbone, one on each side of the hospital.
The diameter (typically 9/125 micrometer) and structure of each cable determines the speed of data transmission (band-width) which is measured in quantity of data per unit time (e.g. bits/sec). Core cables capable of delivering at the speed of 10 Gigabits per second are standard. The backbone is extended at the access level, with multimode cables consisting of four-core (50/125 micrometer) cables capable of delivering at the speed of 10 / 100 / 1000 megabits per second.
The network architecture can be designed as depicted below:System Management Software
Domain Controller In the HIS system as described here, the domain controller (DC) enables the user to access the right ‘domain’ or version of the application or the database i.e.:a. Production or Operations Domain
b. Analytical Domain
c. Build or Test Domain
d. Train DomainThe right of access to a domain is determined by setting privileges. The controller authenticates the user (by username and password). If the MS Windows OS is used then the main part of the controller is the Active Directory. Users are given access to the domain that corresponds to the nature of work to be performed. During training for example the system should be set so that users are directed to the Train Domain. When performing data analysis on historical data then the user uses the Analytical Domain.(this section yet to be edited)Active Directory is, at its heart, a database management system. This database can be replicated amongst an arbitrary number of server computers (called Domain Controllers) in a multi-master manner (meaning that changes can be made to each independent copy, and eventually they’ll be replicated to all the other copies).The Active Directory database in an enterprise can be broken up into units of replication called “Domains”. The system of replication between server computers can be configured in a very flexible manner to permit replication even in the face of failures of connectivity between domain controller computers, and to replicate efficiently between locations that might be connected with low-bandwidth WAN connectivity.Windows uses the Active Directory as a repository for configuration information. Chief amongst these uses is the storage of user logon credentials (usernames / password hashes) such that computers can be configured to refer to this database to provide a centralized single sign-on capability for large numbers of machines (called “members” of the “Domain”).Permissions to access resources hosted by servers that are members of an Active Directory domain can be controlled through explicit naming of user accounts from the Active Directory domain in permissions called Access Control Lists (ACLs), or by creating logical groupings of user accounts into Security Groups. The information about the names and membership of these security groups are stored in the Active Directory.The Domain controller may reside on a separate computer (stand-alone) or within the main server but it would be the intermediary between the front end and the server.
System Manager
(this section is to be edited)
A domain is created strictly for IT management purposes. No access is given to HIS patient data. Access to sensitive information such as configurations of different devices in (servers, applications, network devices, storage devices), access credentials, SNMP settings and Access control list will be strictly controlled using suite of Network Management System consisting of Network Configuration Manager, Storage Manager, Virtualization Manager etc. (e,g SolarWinds or ManageEngine)). Privilege will be segregated based on job category and individual person. System Administrator staff Roles, Permissions, and Activity Tracking available in the same application will be used to protect against unauthorized network configuration changes and ensures compliance with regulations, such as HIPAA and PCI with our change management software. Authentication of administrators and users will be collected from a domain which is strictly used for IT purposes.
This article is in complete and in the process being written








Just fantastic. As a Ph.D. computer science student, I enjoyed reading every single section.
LikeLike
Thank you for reading my article. I am glad you find it interesting. I will relook and see whether I can improve on it.
LikeLike
Hello Dr. Salleh. Thank you for the comprehensive work. Can you please provide some information about connecting a typical HIS System to the cloud and explain the security measures that need to be taken into consideration? (Perhaps with a diagram). Thank you.
LikeLike
I will try to write an article on it. At the moment I trying to write on Mortality Review as requested by a reader from Ethiopia which will finish soon.
LikeLike
Thank you Dr Abdollah! Your article helps me a lot in understanding about HIS system architecture and completing my assignment. I can’t find such comprehensive info on this topc elsewhere. Hope Dr will keep writing… I noted some parts are still incomplete but I will wait… Thanks again!
LikeLike
I am a pharmacist taking health informatics course.
LikeLike
I just found this article. Thanks for the sharing. Very appreciate & many thanks if you could share the article HIS in cloud. Cheers
LikeLike
I just found this article. Thanks for the sharing. Very appreciate & many thanks if you could share the article HIS in cloud. Cheers
LikeLike
Hello Dr Abdollah,
can u provide the details or any link about the real devices with the specifications that are using in this network ?
LikeLike
In the past I have written proposals for systems. Give me some time to look for the documents and I will get back to you. Give me your e-mail address if possible. Mine is drdollah@gmail.com .
LikeLike